HashiCorp Vault's AI Agent Support: Identity, Authorization, and Ephemeral Controls
Traditional IAM systems are built for predictable users and workflows, but the rise of autonomous AI agents introduces new security challenges. These non‑deterministic actors require a fundamentally different authorization model—one that combines identity, delegation, runtime policy evaluation, and ephemeral authorization. HashiCorp Vault now offers purpose‑built capabilities for AI agents, including an agent registry, granular identity‑based policies, and per‑request authorization controls. Below, we answer common questions about this new support.
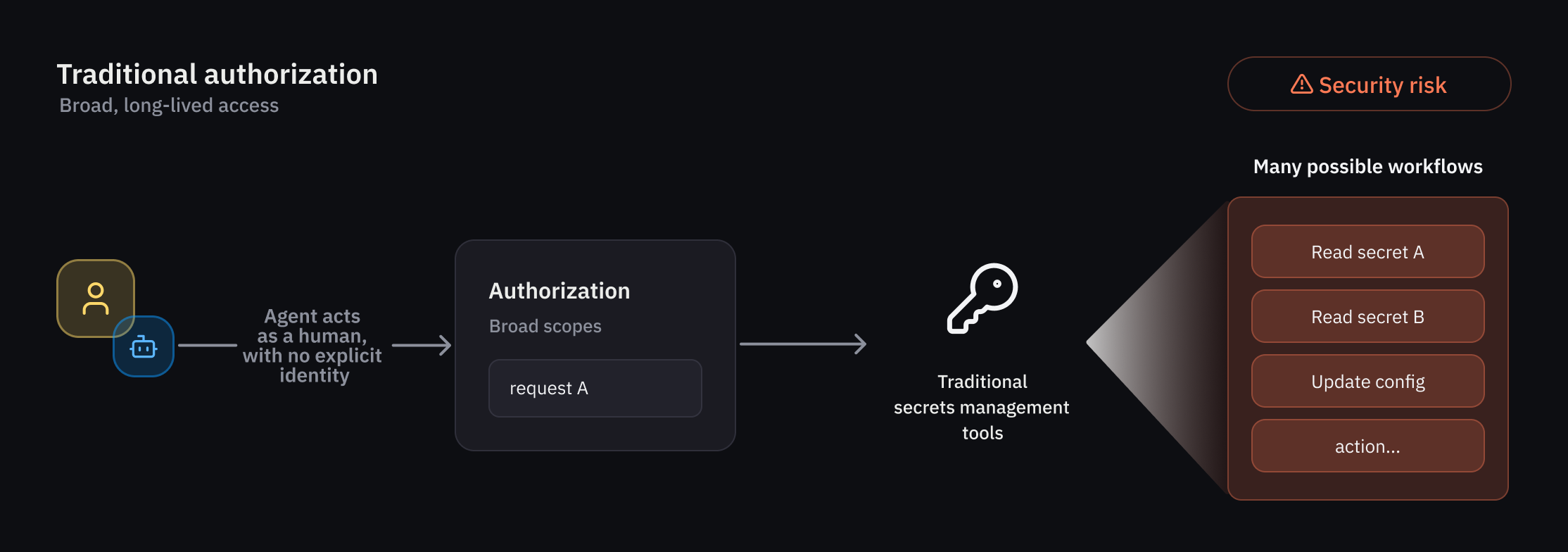
Why can't traditional IAM handle AI agent authorization?
Traditional IAM was designed for deterministic users and workflows—humans or scripts that follow predictable patterns. AI agents, on the other hand, are autonomous and non‑deterministic: they can decide actions on the fly, change course, and delegate tasks without a fixed script. This unpredictability makes static, role‑based access controls insufficient. Agents need temporary, tightly scoped authorization that maps to their identity and the specific context of each request. Traditional IAM lacks the real‑time evaluation and ephemeral credential management required to safely govern agent activity, which is why HashiCorp Vault introduces a new suite of controls specifically for AI agents.
What new capabilities does Vault offer for AI agents?
Vault now includes three core capabilities designed for AI agent workflows: an agent registry to manage agent identities separately from human and non‑human identities; granular identity‑based policies that enforce deterministic guardrails even for non‑deterministic behavior; and per‑request (ephemeral) authorization that grants temporary access rights that expire after a specific task or timeframe. These features also provide clear attribution and auditability for actions performed on behalf of users, ensuring that every agent action can be traced back to its source. An early access program is underway, with a public beta planned for summer.
How does the agent registry work and why is it important?
The agent registry is a new primitive in Vault that allows developers to register and manage AI agent activity separately from human identities and traditional non‑human identities (NHIs). This separation is critical because AI agents often operate in delegation mode, using an on‑behalf‑of (OBO) pattern where they act with the authority of a human user. The registry explicitly tracks this delegation, ensuring it is recorded and auditable. It forms the starting point for a dedicated framework of registration, authorization, credential management, and observability. Without this distinct identity layer, it would be impossible to attribute agent actions accurately or enforce agent‑specific policies.
How does Vault enforce granular identity-based policies for agents?
Least privilege access is a top priority, and Vault addresses it through a rich set of policy‑based runtime controls. Because agent behavior can be non‑deterministic, Vault applies deterministic guardrails—rules that constrain what an agent can do, no matter what path it takes. These guardrails are evaluated at runtime and can be scoped to individual actions or workflows. For example, a policy might allow an agent to read secrets only if it has a valid delegation token from a specific user and the request originates from a trusted IP range. This ensures that even if an agent behaves unpredictably, it cannot exceed the limits defined by administrators.
What is per-request (ephemeral) authorization and how does it reduce risk?
Per‑request authorization, also called ephemeral authorization, grants temporary access rights that expire immediately after a specific task or timeframe—often within seconds. Instead of issuing long‑lived credentials, Vault issues a token that is valid only for the duration of a single API call or a short workflow. This drastically reduces the risk of credential misuse or lateral movement. If an agent is compromised, the attacker only gains access to that single request, nothing more. Ephemeral authorization also eliminates the need for secret rotation, as each credential is created fresh and destroyed automatically. It aligns perfectly with the transient nature of AI agent operations.
How does Vault handle delegation and on-behalf-of (OBO) patterns?
AI agents frequently use an on‑behalf‑of (OBO) pattern where they act with the delegated authority of a human user. Vault evaluates trust across multiple dimensions in this mode: the agent's identity, the human user's identity, the scope of delegation, and the context of the request. The agent registry ensures that this delegation is explicitly tracked and auditable. When an agent requests access, Vault checks whether the agent is authorized to act on behalf of that user and whether the requested action falls within the delegated permissions. This multi‑dimensional trust evaluation allows organizations to maintain clear attribution—every action is tied to both the agent and the human who delegated authority.
When will Vault's AI agent features be generally available?
HashiCorp is currently running an early access program with select customers who are evaluating these new capabilities. Feedback from this program will help refine the features before a broader public beta release, which is planned for summer. The timeline for general availability (GA) will be announced after the beta phase. Organizations interested in participating in the early access program can reach out to HashiCorp directly. Once released, these capabilities will be available as part of HashiCorp Vault, providing a standardized approach for securing AI agents across environments and workflows.